Budget-friendly WordPress hosting doesn’t have to mean slow speeds or limited features. Many providers offer reliable performance, strong security, and the tools you need to grow — all at a price that will make you smile. If you’ re starting a new site or running a small business, the…
Jetpack
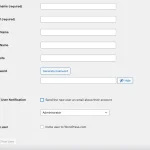
How to Change Your WordPress Admin Username
Security and ease of use are critical aspects of any WordPress site, but it can be easy to sacrifice one in favor of the other. For example, site owners tend to leave default usernames in place, such as “admin, ” rather than setting a new one, which inadvertently leaves…
The 6 Best Ways to Prevent Spam Form Submissions in 2025
As a website owner, you don’t want to be inundated with spam form submissions. But at the same time, you also don’t want to scare off legitimate inquiries with frustrating spam prevention protocols. So how can you prevent spam without drying up your pipeline? The answer lies in…
The 6 Best Translation Plugins for WordPress (Including Auto-Translation)
Expanding your WordPress site to multiple languages shouldn’t be a hassle. Whether you run an ecommerce store, a multilingual blog, or a business with international clients, the right translation plugin removes language barriers without creating more work for you. Manually translating content takes time and professional translation services…
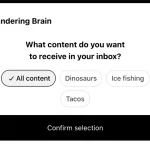
New with Newsletter: Categories and Subscriber Management
We’ve been busy developing new features that make creating, managing, and growing your newsletter with Jetpack easier. These features give you more control and better insights into your audience. As a reminder, every Jetpack site includes Newsletter, granting you the ability to send new posts via email to subscribers….
How to Create a Blog on WordPress: Beginner’s Guide with Top Tools
Starting a blog on WordPress is one of the best ways to share your ideas, showcase your expertise, or even generate additional income. WordPress provides flexibility, scalability, and an extensive set of tools to create, manage, and grow your blog efficiently. This guide will walk you through every…
Jetpack Account Protection: Effortless Password Security
Tired of playing password roulette with your WordPress site? We get it. A weak password is like leaving your front door wide open to digital troublemakers. But don’t worry; Jetpack’s got you covered. Our new free Account Protection feature makes creating strong passwords easy and slams the door…
What is a WordPress Taxonomy? How to Add Custom Taxonomies
Organizing content efficiently is crucial for both user experience and site management purposes. And for WordPress sites, taxonomies play a pivotal role by grouping related content together. This guide covers the concept of WordPress taxonomies, explores the default options, and provides a step-by-step approach to creating custom taxonomies….
WordPress Image Sizes: Recommended Dimensions & Resolutions
Optimizing image sizes in WordPress is an essential part of maintaining a fast-loading and user-friendly website. Image files are one of the biggest contributors to poor website performance. The more images you have and the larger they are, the slower your website will be to load. Properly sized…
How to Easily Manage Multiple WordPress Sites (Top 8 Tools)
Since WordPress is a very user-friendly CMS, managing a single site is usually pretty straightforward. But if you’re in charge of several (or several hundred), you’re probably always looking for ways to streamline common workflows. At a minimum, you’re likely tasked each month with keeping software up-to-date, ensuring…
The 5 Best Blogging Platforms to Elevate Your Presence in 2025
Starting a blog is one of the most effective ways to share your ideas, connect with others, and build a lasting presence online. Blogs help grow businesses, build personal brands, and offer an avenue for sharing your expertise. However, before you can put words on a page, you…
The 9 Best WordPress Newsletter Plugins (Free & Paid)
Are you ready to turn your WordPress site into a powerful email marketing tool? To get started, you’ll need a newsletter plugin. This post introduces you to the best options on the market, both free and paid. It also shows you what to look for when choosing a…
How to Measure Content Performance & Which Metrics to Track
You pour hours into your content — but is it getting results? Uncertainty makes it tough to refine your strategy or prove your content program is worth the effort. Without knowing how to measure performance, you’ re basically flying in the dark. Fortunately, modern analytics tools make it simple…
Seamless Bluesky Sharing with Jetpack Social: Expanding Your Blog’s Reach
Getting your words in front of the right audience is half the battle. Jetpack Social has made this process smoother than ever, especially when sharing your WordPress blog posts to Bluesky. Why Bluesky Matters for Content Creators Bluesky has quickly become a haven for writers, journalists, and content…
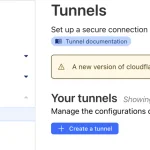
Local Jetpack Development with Cloudflare Tunnel
There are many features of Jetpack that are only available when its connection to WordPress.com is active. This affects the Jetpack development environment, where enabling the Jetpack connection may not always be straightforward. To overcome firewalls and network limitations, tools like ngrok or reverse SSH tunnels are usually…